IoT & Embedded Technology Blog
AWS IoT Forging Ahead with Long List of New Features
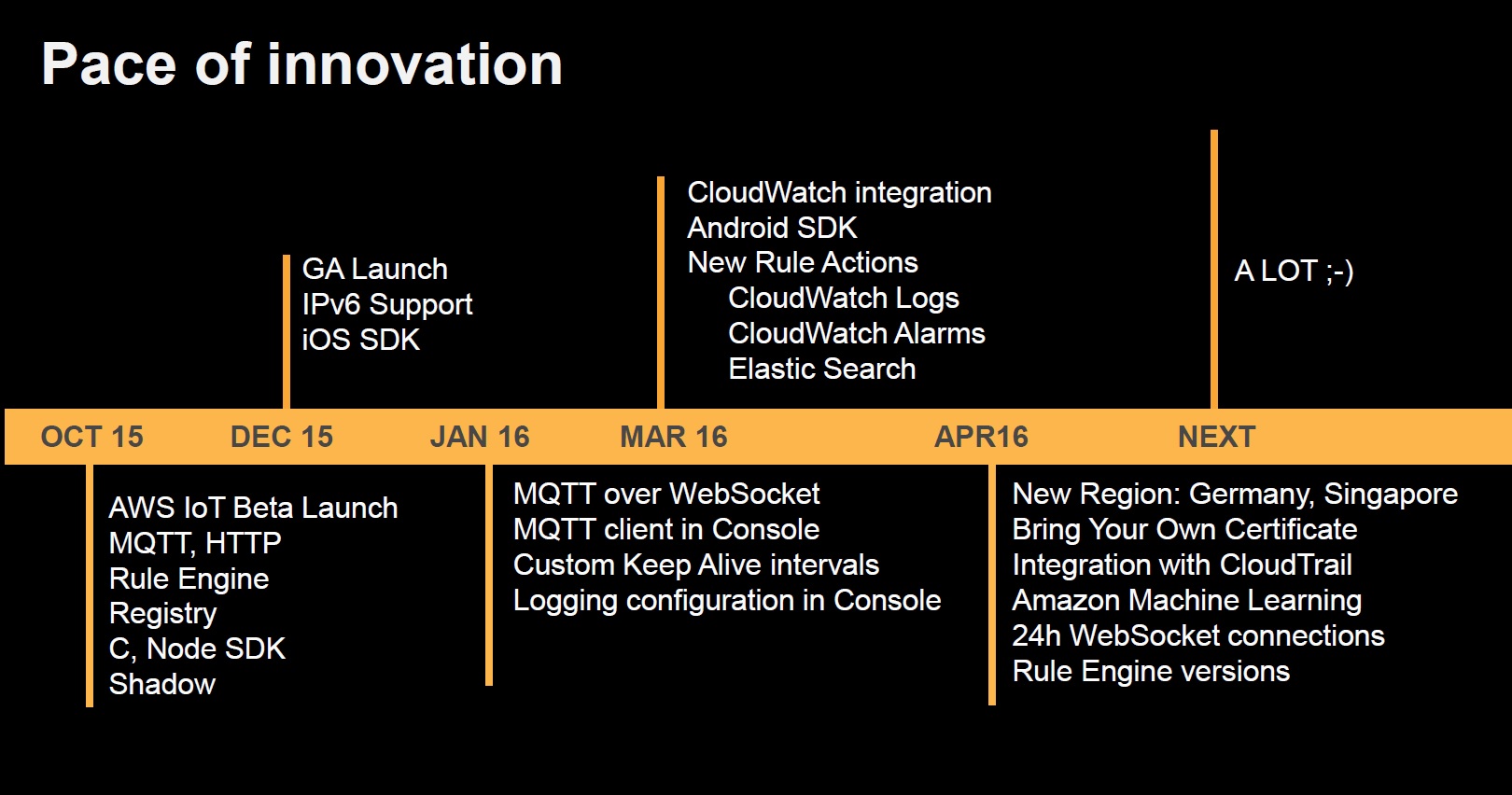
The AWS IoT team has been remarkably busy over the past few months. Antony Passemard, Head of Product Management at AWS IoT, sat down with me yesterday to discuss AWS IoT’s latest enhancements. The following list of recently-added capabilities and features paints a clear picture of the pressing issues faced by cloud platform providers and their customers.
1) Security, Security, Security: “Bring Your Own Certificate” and Cryptochips
With connectivity comes insecurity. While this concept is not exactly earth-shattering, it remains top of mind for the majority of IoT product manufacturers and end users that are looking to connect their devices, systems, and networks to the Internet.
To this end, AWS IoT has taken a huge step forward by supporting a “Bring Your Own Certifice” (BYOC) policy. Previously, customers using MQTT had to rely on AWS IoT to generate a X.509 certificate, which was then downloaded by the user along with the public and private keys associated with that certificate. While the key download was always initiatied over a TLS-secured connection, making snooping/interception very difficult, this still represented a possible (if somewhat unlikely) point of failure in the security of the system.
The new update allows customers to use their own certificate authority to upload an unlimited number of pre-issued certificates to the platform, which removes the need for customers to download their keys from Amazon. BYOC removes this possible point of failure, giving customers the ability to add another layer of security to their authentication architecture. The team has added eight new API calls to support BYOC management.
Additionally, AWS IoT has added support for elliptic curve Diffie-Hellman key exchange (ECDHE) TLS cipher suites that are faster, lighter, and more secure than the previously-used RSA-based suites. ECDHE also enables the use of newer “cryptochips” such as Atmel’s ATECC508A. These cryptochips are tiny, inexpensive, low-power chips that can be easily designed into IoT nodes and used for the express purpose of secure authentication. The cryptochip employs hardware-based key storage which is more secure than traditional software-based key storage, and which also removes the node ECU’s burden of processing TLS handshakes. Intel and Broadcomm are also building similar cryptochips which will be commonly used in IoT security architectures going forward.
2) Tighter AWS Integration
The AWS IoT has added more Cloudwatch actions and alerts, which will give users a richer set of triggers and alarms to use when building rules across their entire AWS platform. Somewhat in tandem, the team has also integrated its Elasticsearch service, which lets customers route device-generated data directly to Elasticsearch domains, which are generally used to perform rich analytics and data visualizations through Kibana, a popular open-source tool. Additionally, a new predict function allows customers to call Amazon machine learning models to fill in values or create predictions based on streams of data that were previously fed into the Amazon Machine Learning service.
3) Miscellanea: Lifecycle Events, Versioning Control, Geographic Coverage
Users can now build “presence platforms” with the addition of the Connect and Disconnect events, which will allow for on-the-fly certificate acceptance as devices connect to the service, among other things. Antony also gave an example of a customer that is building an instant messaging platform that needs access to device state data in order to accurately deliver messages.
Versioning control will allow customers to ensure that they are running a version of AWS IoT where their rules will not be automatically broken/deprecated as AWS IoT innovates and releases updates to the rules engine and platform.
AWS IoT also launched in Germany and Singapore last month, where customers were requesting the service due to geography-based data privacy laws. Major users in these new sectors include large healthcare and manufacturing organizations, unsurprisingly.
Summary
It is clear that AWS IoT is innovating at a rapid pace, but a more important question is whether the platform is moving in the right direction.
We believe that by focusing on enabling platform support for its next-generation security and privacy technologies, AWS IoT is firmly and intelligently addressing one of the largest hurdles to adoption in the marketplace today.
As for the added functionality – customers will no doubt welcome the ever-expanding functionality of the service as it emerges from its infancy. One of the things that we appreciated in our recent breakdown of AWS IoT and Azure IoT Hub (download here) was the relative simplicity and focused nature of AWS IoT’s offering. The team will need to be careful not to swamp its customers with too much choice, which could bury potentially useful upgrades among a torrent of added plugins, rules, and functionality.
We look forward to continuing our coverage of the fierce competition in this new and exciting IoT message routing segment within the rapidly-growing IoT services market.